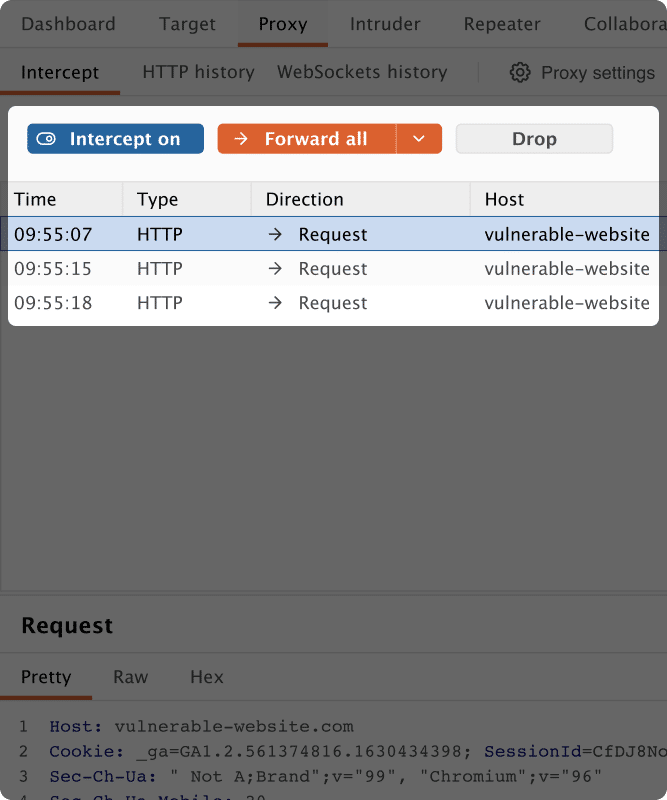
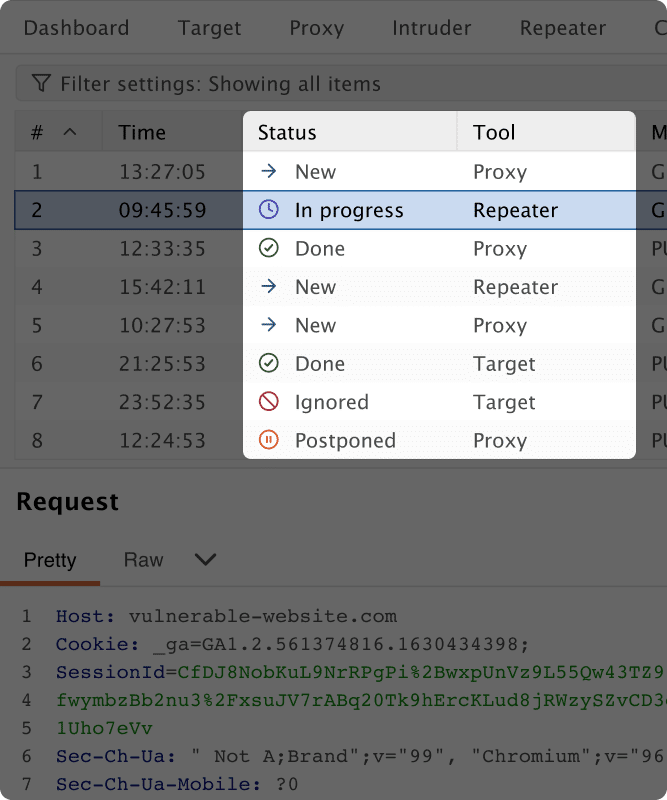
“Checking out the new Bambdas for proxy filtering that
Burp Suite just launched. Quickly parsing through all my
history to identify improperly set Content-Types. It
will definitely come in handy to be able to create these
powerful filters from now on!”Carles Llobet Pons, Cyber Security Professional.